
Envoi et réception sécurisés des messages par iMessage
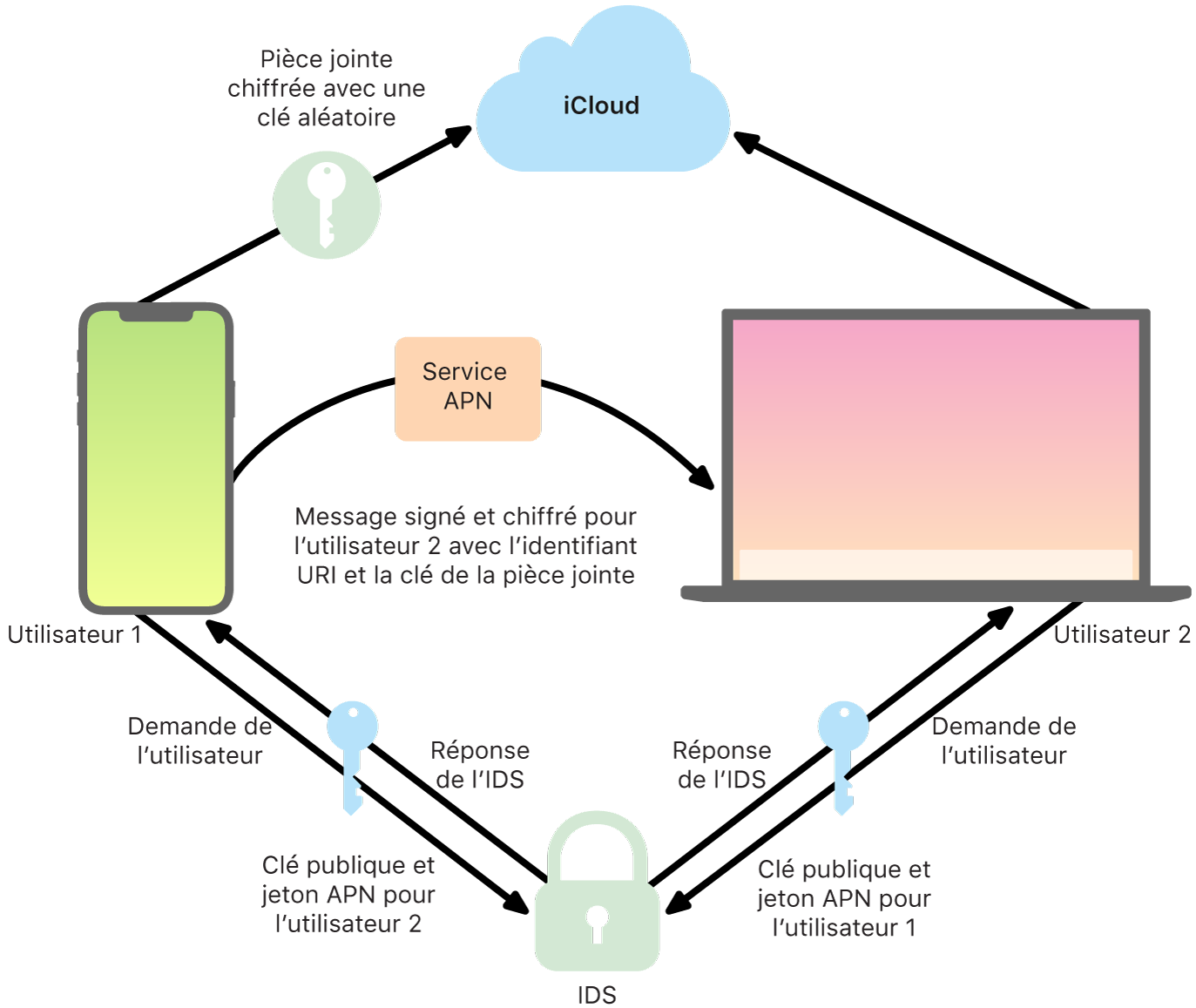
L’utilisateur lance une nouvelle conversation iMessage en saisissant une adresse ou un nom. S’il saisit un numéro de téléphone ou une adresse électronique, l’appareil entre en contact avec le service d’identité d’Apple (IDS) pour récupérer les clés publiques et les adresses de service APN de tous les appareils associés au destinataire. Si l’utilisateur saisit un nom, l’appareil utilise d’abord l’app Contacts de l’utilisateur pour récupérer les numéros de téléphone et les adresses électroniques associés à ce nom, puis récupère les clés publiques et les adresses de service APN à l’aide du service IDS.
Le message sortant envoyé par l’utilisateur est chiffré séparément pour chacun des appareils du destinataire. Les clés de chiffrement et de signature publiques des appareils récepteurs sont récupérées par l’entremise de l’IDS. Pour chaque appareil récepteur, l’appareil émetteur génère une valeur 88 bits aléatoire et l’utilise comme clé HMAC‑SHA‑256 pour construire une valeur 40 bits dérivée de la clé publique et du texte brut de l’expéditeur et du destinataire. La concaténation des valeurs 88 bits et 40 bits crée une clé 128 bits, qui chiffre le message à l’aide de l’algorithme AES en mode CTR (basé sur un compteur). Cette valeur 40 bits est utilisée par le côté récepteur pour vérifier l’intégrité du texte brut déchiffré. Cette clé AES propre à chaque message est chiffrée via RSA‑OAEP vers la clé publique de l’appareil récepteur. La combinaison constituée du texte du message chiffré et de la clé de message chiffrée est ensuite hachée avec l’algorithme SHA‑1, et le hachage est signé avec l’algorithme ECDSA (Elliptic Curve Digital Signature Algorithm, algorithme de signature numérique basé sur les courbes elliptiques) à l’aide de la clé de signature privée de l’appareil émetteur. Sur les iPhone sous iOS 13 ou les versions ultérieures ou sur les iPad sous iPadOS 13.1 ou les versions ultérieures, les appareils peuvent utiliser un chiffrement intégré basé sur les courbes elliptiques (ECIES) au lieu d’un chiffrement RSA.
Les messages résultants (un pour chaque appareil récepteur) sont constitués du texte de message chiffré, de la clé de message chiffrée et de la signature numérique de l’expéditeur. Ils sont ensuite transmis au service APN en vue de leur livraison. Les métadonnées, comme les données d’horodatage et les informations de routage du service APN, ne sont pas chiffrées. La communication avec le service APN est chiffrée par l’intermédiaire d’un canal TLS à confidentialité persistante.
Le service APN ne peut relayer que des messages de 4 ko ou 16 ko, selon la version d’iOS ou d’iPadOS. Si le texte du message est trop long ou s’il contient un fichier, comme une photo, la pièce jointe est chiffrée par AES en mode CTR à l’aide d’une clé 256 bits générée aléatoirement, puis est téléversée vers iCloud. La clé AES destinée à la pièce jointe, son identifiant de ressource uniforme (URI) et un hachage SHA‑1 de sa forme chiffrée sont ensuite envoyés au destinataire en tant que contenu de message iMessage, la confidentialité et l’intégrité de ces éléments étant protégées par un chiffrement iMessage normal (voir l’illustration suivante).
Dans le cas d’une conversation de groupe, ce processus est répété pour chaque destinataire et ses appareils.
Du côté du destinataire, chaque appareil reçoit sa copie du message via le service APN et, si nécessaire, récupère la pièce jointe sur iCloud. Le numéro de téléphone ou l’adresse électronique de l’expéditeur est comparé aux données figurant dans les contacts du destinataire afin de pouvoir afficher un nom si possible.
Comme pour toutes les notifications de type Push, le message est supprimé du service APN dès sa livraison. Contrairement à d’autres notifications du service APN, les messages iMessage sont placés en file d’attente en attendant d’être livrés à des appareils déconnectés. Les messages sont conservés sur les serveurs Apple pendant 30 jours au maximum.