
Apple Business Manager User Guide
Apple Business Manager is now Apple Business
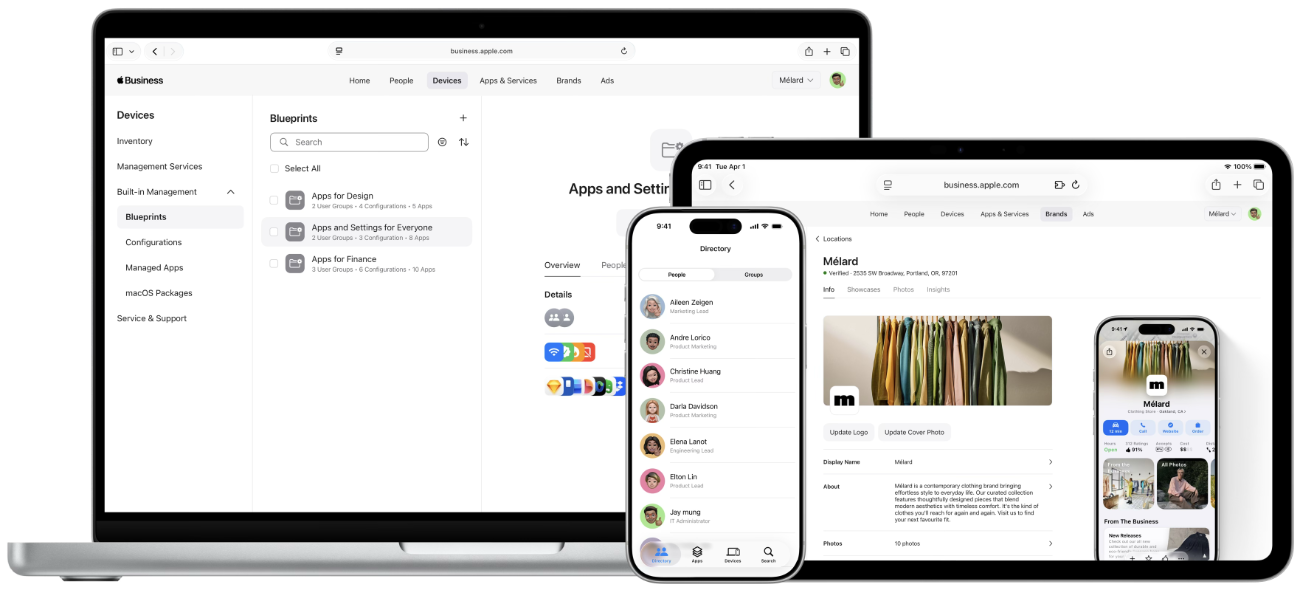
Apple Business combines the capabilities previously found in Apple Business Manager, Apple Business Essentials and Apple Business Connect into a single, comprehensive offering, catering to both your internal operational needs and your external customer-facing strategies.