
Use federated authentication with Microsoft Azure AD in Apple Business Manager
In Apple Business Manager, you can link to Microsoft Azure Active Directory (Azure AD) to allow users to sign in with their Azure AD username and password.
Azure AD is the identity provider (IdP) that authenticates the user for Apple Business Manager and issues authentication tokens. This authentication supports certificate authentication and two-factor authentication (2FA). Because Apple Business Manager supports Azure AD, other IdPs that connect to Azure AD – like Active Directory Federation Services (AD FS) – will also work with Apple Business Manager.
Important: Federated authentication requires that a user’s User Principal Name (UPN) match their email address. User Principal Name aliases and Alternate IDs aren’t supported.
Federated authentication and directory sync with Microsoft tenants
To add the Apple Business Manager Azure AD app with Microsoft tenants, the administrator of the tenants must go through the federated authentication setup process, including testing authentication. When authentication has succeeded, the Apple Business Manager Azure AD app is populated in the tenant and the administrator can federate domains and configure Apple Business Manager to use SCIM (System for Cross-domain Identity Management) for directory sync. See Review SCIM requirements.
Before you begin
There is a three-step process to link Apple Business Manager to Azure AD and use federated authentication:
Add and verify a domain. See Link to new domains.
Multiple domains can be federated, but they must be from the same single public tenant. If you’re attempting to federate a domain you’ve already verified but another organisation has already federated the identical domain, you must contact that organisation to determine who has the authority to federate the domain. See About domain conflicts.
Configure the federated authentication process.
Test authentication with a single Azure AD domain account.
Configure the federated authentication process
This task allows Azure AD to trust Apple Business Manager.
In Apple Business Manager
 , sign in as a user that has the role of Administrator or People Manager.
, sign in as a user that has the role of Administrator or People Manager.Select your name at the bottom of the sidebar, select Preferences
 , then select Accounts
, then select Accounts  .
.Next to Federated Authentication, select Edit, then select Connect.
Select “Sign in with Microsoft,” enter a Microsoft Azure AD Global Administrator, Application Administrator or Cloud Application Administrator account, then select Next.
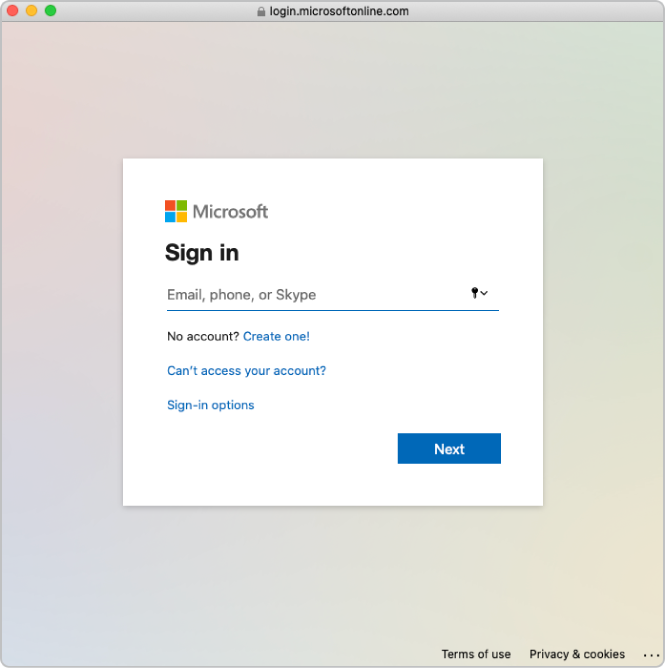
Select “Sign in with Microsoft,” enter a Microsoft Azure AD Global Administrator, Application Administrator or Cloud Application Administrator account, then select Next.
Carefully read the application agreement, then select Accept.
You are consenting to Microsoft giving Apple access to information found in Azure AD.
Select Done.
Note: After you complete this step, users can’t create new personal Apple IDs on the domain you configure. This could affect other Apple services you use. See Transfer Apple services when federating.
In some cases you may not be able to add your domain. Common reasons are:
The Azure AD Global Administrator, Application Administrator or Cloud Application Administrator account used doesn’t have permission to add domains in Microsoft Azure AD.
The username or password from the account in step 4 is incorrect.
Test authentication with a single Azure AD account
This task allows Apple Business Manager to trust Azure AD. After you’ve verified ownership of your domain and successfully tested authentication with a single Azure AD account, you can then create additional accounts and continue federating your domain.
Select Federate next to the domain you want to federate.
Select “Sign in to Microsoft Azure Portal,” then enter your user name and password.
Enter a Microsoft Azure AD Global Administrator, Application Administrator or Cloud Application Administrator account that exists in the domain, then select Next.
Enter the password for the account, select Sign In, select Done, then select Done.
In some cases you may not be able to sign in to your domain. Here are some common reasons:
The username or password from the domain that you chose to federate is incorrect.
The account isn’t in the domain that you chose to federate.
After sign-in is successful, Apple Business Manager checks for username conflicts with this domain. The check for username conflicts must be complete before you can use federated authentication with this domain.
Note: After you successfully link Apple Business Manager to Azure AD, you can change the role of an account to another role. For example, you may want to change the role of an account to a Staff role.
Enable federated authentication
Before you turn on federated authentication, make sure you’ve linked to a new domain and verified it.
Note: If you’re planning on connecting to Azure AD using SCIM, you should wait to turn on federated authentication until after the SCIM connection is successful.
In Apple Business Manager
 , sign in as a user that has the role of Administrator or People Manager.
, sign in as a user that has the role of Administrator or People Manager.Select your name at the bottom of the sidebar, select Preferences
 , then select Accounts
, then select Accounts  .
.Select Edit in the Domains section, then turn on federated authentication for the domains that have been successfully added to Apple Business Manager.
It may take some time to update all accounts.
Test federated authentication
You can test the federated authentication connection after you’ve performed the following tasks:
You’ve completed a successful connection and verification to your domain.
The check for username conflicts is complete.
The Managed Apple ID default format is updated.
Note: Users with the role of Administrator or People Manager can’t sign in using federated authentication; they can only manage the federation process.
In Apple Business Manager
 , sign in as a user that doesn’t have an Administrator role.
, sign in as a user that doesn’t have an Administrator role.If the username you signed in with is found, a new screen indicates that you’re signing in with a user in your domain.
Select Continue, enter the password for the user, then select Sign In.
Sign out of Apple Business Manager.
Note: Users can’t sign in to iCloud.com unless they first sign in with their Managed Apple ID on another Apple device.