OS X Server: How To Configure RADIUS Server Trust in Configuration Profiles when using TLS, TTLS, or PEAP
This article explains how to set trust properly when using configuration profiles.
In OS X, configuration profiles are used to configure a client to join 802.1x protected networks. If the configuration profile does not properly configure trust to the RADIUS server(s) for EAP types that establish a secure tunnel (TLS, TTLS, PEAP) you may see one of the following issues:
inability to auto-join
authentication failure
roaming to new access points does not work
Before you can configure trust properly, you must know which certificates are presented by the RADIUS server during authentication. If you already have these certificates, skip to step 13.
EAPOL logs display the certificates presented by the RADIUS server. To enable EAPOL logs in Mac OS X, use the following command in Terminal:
sudo defaults write /Library/Preferences/SystemConfiguration/com.apple.eapolclient LogFlags -int -1After enabling EAPOL logs, manually connect to the 802.1x protected network. You should be prompted to trust the RADIUS server certificate. Trust the certificate for authentication to complete.
Locate the EAPOL logs.
- In OS X Lion and Mountain Lion, these logs can be found in /var/log/. The log will be called eapolclient.en0.log or eapolclient.en1.log.
- In OS X Mavericks, these logs can be found in /Library/Logs/CrashReporter/com.apple.networking.eapol.XXXXXXXX .
Open the eapolclient.enX.log in Console and locate a key called TLSServerCertificateChain. It should look like this:
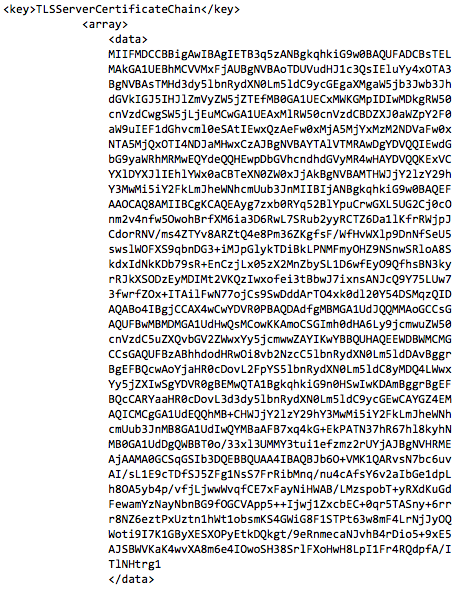
The block of text between
<data>and</data>is a certificate. Copy the block of text and then paste it into a text editor. Make sure your text editor is configured to save plain text files.Add a header of
-----BEGIN CERTIFICATE-----and a footer of-----END CERTIFICATE-----. It should look like this: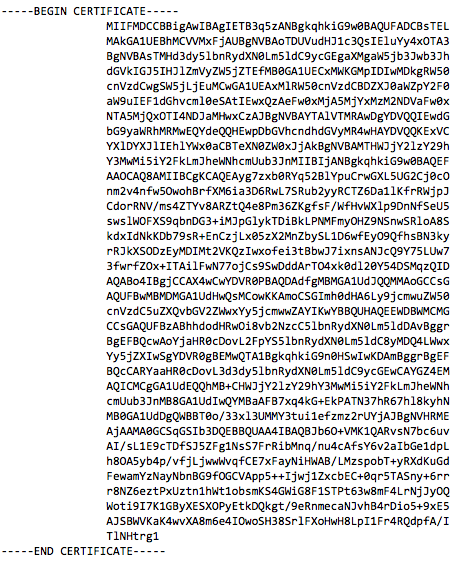
Save the file with an extension of .pem.
Open the Keychain Access app in the Utilities folder.
Note: It may be helpful to create a new keychain so that you can easily find the certificate you import in the next step.
Either drag the .pem file you created into your new keychain, or choose File > Import Items and select the .pem file you created earlier. Import the file into the keychain of your choice.
Repeat the above steps for each certificate in the TLSCertificateChain array. You will likely have more than one certificate.
Inspect each certificate that was imported so you know what it is. At the minimum, you should have a root certificate and a RADIUS server certificate. You may also have an intermediate certificate. You must include all of the root and intermediate certificates presented by the RADIUS server in the Certificates payload in your configuration profile. Including the RADIUS server certificate(s) is optional if you include your RADIUS server names in the Trusted Server Certificate Names section of the Network payload. Otherwise, include the RADIUS server certificate(s) in the profile as well.
Once you know which certificates are presented by the RADIUS server, you can export them as .cer files from Keychain and add them to the configuration profile. Add each of the root and intermediate certificates to the Certificates payload in your configuration profile. You can also add the RADIUS server certificate(s) if needed.
In the Network payload, locate the Trust section and mark the certificates you just added as trusted. Be sure that you don't mark any other certificates that may also be in the Certificates payload as trusted, or authentication will fail. Make sure to only mark the certificates actually presented by your RADIUS server as trusted.
Next, add the names of your RADIUS servers to the Trusted Server Certificate Names section. It is required that you use the exact name (including case) that appears as the common name of your RADIUS server certificate. For example, if the common name of your RADIUS server certificate is TEST.example.com, you must be sure to match the case that is used in the certificate. The value "test.example.com" would not be valid, but "TEST.example.com" would. You must add a new entry for each of your RADIUS servers. You may also use a wildcard for the hostname. For instance, *.example.com would cause all RADIUS servers on the domain example.com to be trusted.
If you previously enabled eapol logs, you can disable the logging with the following command:
sudo defaults write /Library/Preferences/SystemConfiguration/com.apple.eapolclient LogFlags -int 0
If you aren't sure if trust is configured properly, you can check /var/log/system.log. Open system.log in Console and filter on "eapolclient" to see all messages related to the eapolclient process. A typical trust error looks like this:
Mar 31 12:27:14 Macintosh.local eapolclient[5961]: [eapttls_plugin.c:968] eapttls_verify_server(): server certificate not trusted status 3 0